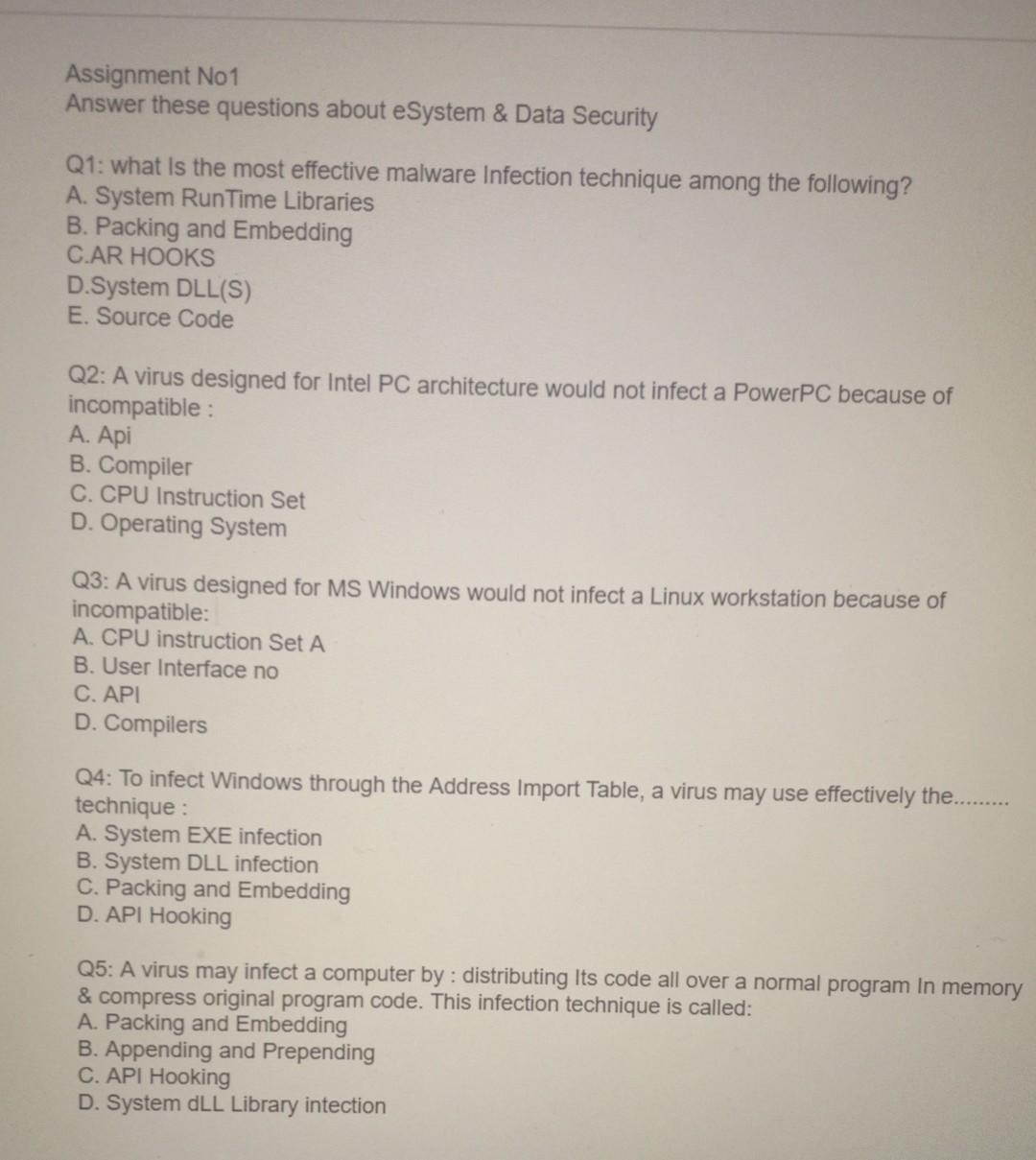
PDF) Usefulness and problems of the urinary tract infection criteria for evaluating drug effi cacy for complicated urinary tract infections | Katsumi Shigemura - Academia.edu

Cpu on board with cyber attack hologram. Cyber attack hologram over working cpu in background. danger alert, threat, | CanStock

Cyber attack and skull glowing hologram over working cpu in background. Danger alert, threat, infection and warning abstract concept with skull symbol Stock Photo - Alamy

Cpu On Board With Cyber Attack And Skull Hologram Stock Photo - Download Image Now - Blue, CPU, Computer - iStock

Cpu On Board With Cyber Attack And Skull Hologram Stock Photo - Download Image Now - Blue, CPU, Computer - iStock

Pichia-secreted mVHH-IgA prevents F4-ETEC infection in piglets a,b,... | Download Scientific Diagram

Cyber attack and skull glowing hologram over working cpu in background. Danger alert, threat, infection and warning abstract concept with skull symbol Stock Photo - Alamy